[ad_1]
Howdy folks,
In our first blog of this series, we discussed general availability of custom roles for delegated app management. Continuing the series of announcements for Azure Active Directory (Azure AD) role-based access control (RBAC), I’m excited to share several new features to enable fine-grained delegation of device administration in Azure AD. With these new capabilities, you can now:
- Create custom roles using permissions for device objects.
- Add devices as members of administrative units and assign built-in or custom roles for managing devices over the scope of an administrative unit.
Let’s take a look at some of the cool things you can do with these new capabilities.
You can also watch and experience these new features in action:
Create a custom role
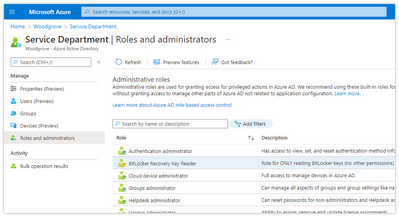
To create a custom role using device permissions, go to Roles and administrators, then select New Custom Role. In this example, we’ll create a custom role called “BitLocker Recovery Key Reader.”
Give the role a name and description. Next, use the new device permissions for custom roles to select only the BitLocker permissions for this role.
Finally, click Next and create the role. Now you have a custom role that you can use to delegate access only to read BitLocker recovery keys without having to grant any unnecessary permissions.
Add devices to an administrative unit
In addition to customizing the permissions in the role, you can also use administrative units to scope those permissions to a specific set of devices.
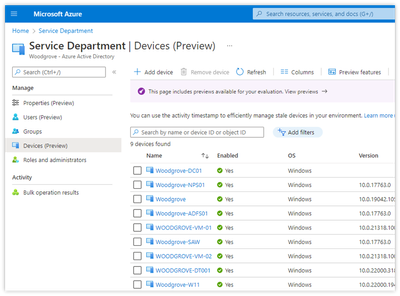
In the example below, devices have been added to an administrative unit called “Service Department.” You can click Add device to add additional device(s) to the administrative unit.
Putting it all together
You can now go to the Roles and administrators tab and assign the custom role you created over the scope of the administrative unit. This allows you to ensure that the BitLocker permissions you specified when you created the role apply only to the devices specified in the administrative unit.
Note: we highly recommend assigning the custom role as an eligible assignment through Privileged Identity Management.
That’s it! For more information, check out our documentation on custom roles or administrative units. You can also access these same capabilities using PowerShell and Microsoft Graph APIs.
What’s next
Stay tuned for more great features around Azure AD RBAC. In the meantime, we’d love to hear your feedback, thoughts, and suggestions. You can share these with us on the Azure AD administrative roles forum or leave comments below.
Best Regards,
Alex Simons (Twitter: @Alex_A_Simons)
Corporate VP of Program Management
Microsoft Identity Division
Learn more about Microsoft identity:
[ad_2]
Source link