[ad_1]
In February 2022, we made an announcement of the public preview of Azure AD Certificate-Based Authentication as a part of Microsoft’s commitment to Executive Order 14028, Improving the Nation’s Cybersecurity .
The public preview process gives us the opportunity to get great feedback from folks who weren’t in the private preview. In this case, we got some great feedback and have added several important features to our existing public preview. Here are some great customer-feedback driven enhancements to Azure AD Certificate Based Authentication (CBA):
- Azure AD CBA support for Windows logon and Single Sign-On (SSO) to Azure AD applications and resources
- Azure AD CBA support for mobile platforms (iOS, Android) for accessing Microsoft’s applications on managed and unmanaged devices
- Improved administration capabilities for managing Trusted Certificate Authorities configuration in Azure AD
- Staged rollout support for CBA for easy and controlled migration from Active Directory Federated Server
Vimala Ranganathan, Senior Product Manager on our Identity team, will walk you through the details.
Thanks,
Alex Weinert, Director of Identity Security, Microsoft
(Twitter: @Alex_t_weinert)
———————————————————–
Hi everyone,
I am Vimala from the Identity PM team, and I am excited to walk you through all the new features we’ve added to the existing public preview of Azure AD (CBA).
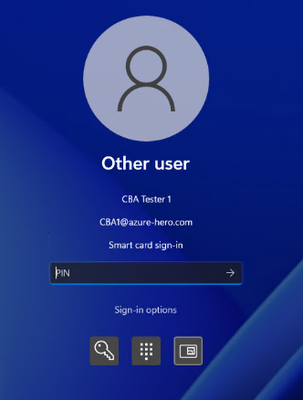
Windows logon support
Azure AD users on Windows 11 (22H2) can now authenticate using X.509 certificates on their smartcards directly against Azure AD at Windows logon. On Azure AD join devices and Hybrid Azure AD join devices, once the user logs into Windows with a certificate, they will get the added benefit of SSO to all applications integrated with Azure AD.
In the future, we will also support this feature in Windows 10 and Windows Server.
Mobile devices (Android and iOS) support
Now you can use Azure AD CBA to authenticate against Azure AD using certificates provisioned on user’s device on iOS and Android devices. Both native browsers and a list of Microsoft applications are supported. Enterprises can use Mobile Device Management (MDM) solutions like Microsoft Intune to provision the client certificates or derived personal identity verification (PIVs) onto the devices they manage.
Here is the list of the supported Microsoft apps:
|
Azure Information Protection app |

|
|
Intune Company Portal |

|
|
Microsoft Teams |

|
|
Office (mobile) |

|
|
OneNote |

|
|
OneDrive |

|
|
Outlook |

|
|
Power BI |

|
|
Skype for Business |

|
|
Word / Excel / PowerPoint |

|
|
Yammer |

|
Improved administrative experience
Making it easier for you to set up and manage CBA configuration is a priority for us. Previously you had to use PowerShell commands to upload the certificate authorities to Azure AD, but now you can seamlessly use the Azure portal to configure certificate authorities.
Using the Azure portal, you can now:
- Upload certificate authorities (root CA and all the intermediate CAs) to Azure AD
- View all the trusted certificate authorities uploaded to the Azure AD
- Delete the CAs if they’re not valid
- Easily see the validity of the certificate based on the certificate expiry date
What’s next
Keep your feedback coming at Azure Active Directory Community! We’re working diligently to bring more enhancements like CBA as a second factor of authentication, removal of limits on Certificate Revocation List (CRL), support for non-routable UPNs, and external smart cards support on mobile devices.
You can learn more about Microsoft’s commitment to Executive Order 14028 here.
Thanks,
Vimala
Learn more about Microsoft identity:
Source link