[ad_1]
We realize that many customers have genuine business requirements to configure automatic email forwarding. On the other hand, email forwarding may lead to data leakage. For example, if we have a compromised account, the attacker might create a forwarding rule for a particular mailbox, and the user might be unaware that their mail is being forwarded. This is a very common tactic used when accounts are compromised.
It is therefore important for administrators to know all mailboxes that have forwarding enabled and where the mail is been forwarded to. We have various insights and alerts that help administrators monitor such activities, but prevention is always better than the cure. In this blog post, we thought to revisit (and update) various auto forward controls, how they work together and how they can help you achieve a requirement of allowing automatic forwarding for users who really need this feature.
Various ways to set up forwarding
Before discussing how to control automatic forwarding, let’s review a few different ways in which automatic forwarding can be setup:
- A forwarding rule can be setup within the Rules wizard in Outlook on the desktop. User can set this Automatic forwarding from Outlook > File > Manage Rules and Alerts. Using Outlook on the web, this can be done using Inbox rules.
- Using Outlook on the web (OWA) the user can also set the ForwardingSmtpAddress parameter on the mailbox. This option is available via Settings > Mail > Forwarding.
- Users can also set auto forward using Power Automate (used to be called Microsoft Flow).
- Administrators can configure forwarding from the properties of the mailbox from Exchange Admin Center. This option is available under “Manage Mail flow settings” in classic EAC, or user properties in the preview version of EAC. Configuring automatic forwarding from the properties of the mailbox will populate the ForwardingAddress parameter on the mailbox.
- Administrators can also configure forwarding from Microsoft 365 Admin Center. Configuring forwarding from Microsoft 365 Admin Center will set the ForwardingSmtpAddress parameter on the mailbox (but will show if ForwardingAddress is populated).
Administrators have several methods to prevent and regulate automatic forwarding of emails outside the organization:
External email forward control using Outbound spam filter policy
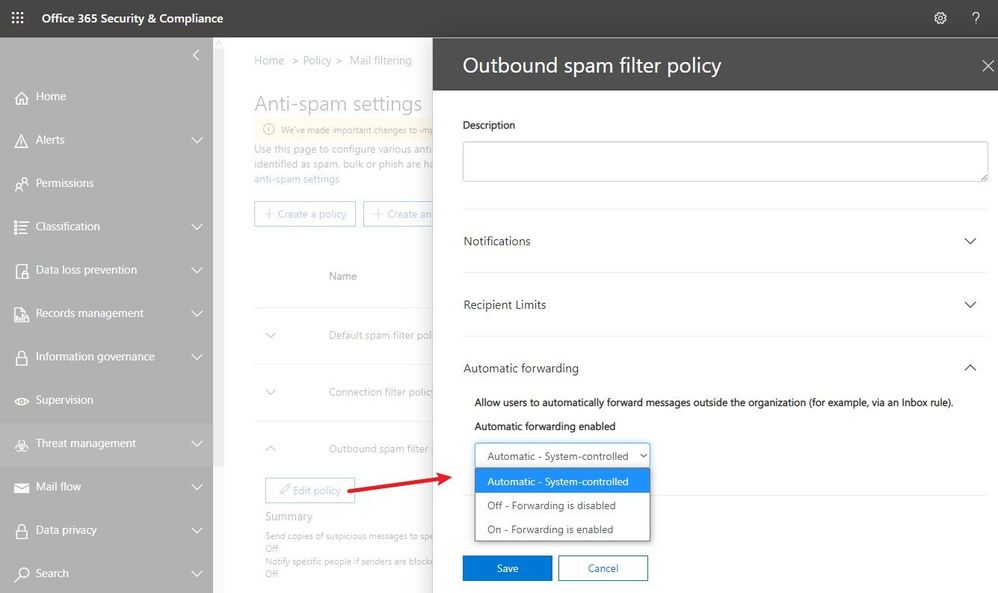
Recently released, this feature is available in Security & Compliance portal under Outbound spam filter policy (to get the exact portal page, go here). As you see in the following screenshot, there are three possible options. The default configuration is “Automatic system-controlled.” Other options are Off and On. “Off” means auto forward is disabled and “On” means auto forward is enabled.
Note: If you see the option is set as “Automatic system-controlled”, most probably you have not configured the setting at all. For tenants where the setting is left at “Automatic system-controlled”, as we continue to move the service toward being more secure by default, this setting will be enforced and behave as “Off” (forwarding disabled). This enforcement process has started in phases and very soon, all tenants will get this setting enforced. Therefore, “Automatic system-controlled” will behave as “Off” and automatic forwarding will not work. Our recommendation is that all customers should configure the policy as appropriate for their organization and enable external auto forwarding only for the users who really need it (by leaving the default policy in disabled state, creating a different policy that allows forwarding and then assigning it to specific mailboxes only). If for your tenant, “Automatic system-controlled” still does not block email forwarding, you should make this change as soon as possible (as soon, it will).
Advantages of this method:
- It blocks all types of auto forwarding including ForwardingAddress and ForwardingSmtpAddress mailbox parameters.
- Blocks redirect rules configured using Outlook.
- A NDR is sent back to the mailbox that configured auto forwarding to external user if the policy is set to block automatic forwarding for that mailbox. The NDR will contain the following diagnostic information:
Remote Server returned ‘550 5.7.520 Access denied, Your organization does not allow external forwarding. Please contact your administrator for further assistance. AS(7550)’
- Easier to configure and administrators can selectively allow/block external auto forwarding for a few or all mailboxes.
Disadvantages of this method:
- Forwarding using Power Automate (Flow) is not covered as of now. To block external forwarding which is setup using Power Automate, follow the steps mentioned in our Email exfiltration controls for connectors article.
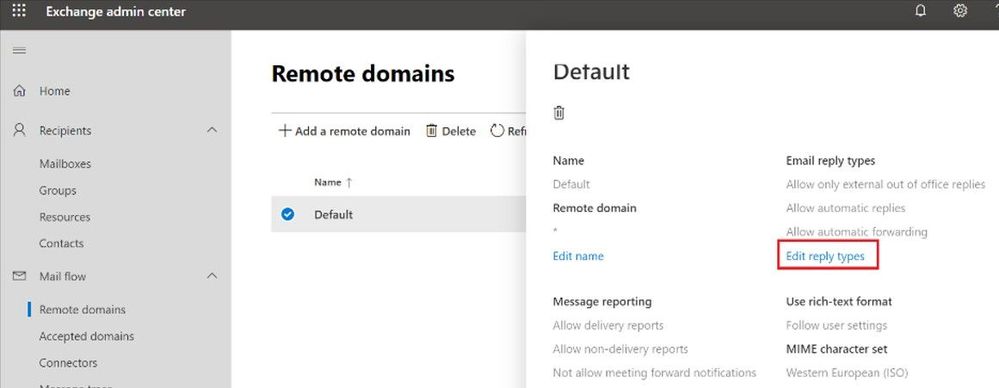
Block automatic forwarding using Remote Domains
This option is available under the Mail flow tab in the new Exchange Admin Center preview:
Advantages of this method:
- This setting can block auto forward rules configured using Outlook inbox rules as well as Outlook on the web options (ForwardingSmtpAddress parameter)
Disadvantages of this method:
- Does not block forwarding set from the properties of the mailbox by the administrator using EAC (ForwardingAddress parameter)
- This blocks auto forward to the specific remote domain. There is no granular control – cannot allow forwarding for certain users, and block for others.
- The user is not notified that their auto forwarded message is dropped, no rejection (NDR) is sent.
Block auto forward using a transport rule
You can create a transport rule from Exchange Admin Center > Mail Flow > Rules to block automatic forward:
Advantages of this method:
- Allows granular control on conditions and actions.
- Admins have the option to send rejection message (NDR).
Disadvantages of this method:
- Matches auto forward messages based on message class (IPM.note.forward). The Outlook web app forwarding (ForwardingSmtpAddress) or forwarding set by the admins on the properties of the mailbox (ForwardingAddress) have normal message class (IPM.Note), so transport rules won’t block them.
- Difficult to manage at times when too many transport rules are configured.
While this is not really a method of blocking forwarding, it is related in a way that it can help remove forwarding options from users if they are using Outlook on the web.
Advantages of this method:
- In OWA, users simply do not see the option to setup forwarding in their mail options
Disadvantages of this method:
- Does not remove the option in Outlook desktop.
- Any forwarding that was already configured will continue to work.
Overview
If you want to quickly compare various methods, you can refer to the following table:
|
Automatic forwarding option |
Remote domain |
Transport rule |
Outbound spam filter policy |
|
Block Outlook forwarding using inbox rules |
Yes |
Yes |
Yes |
|
Block OWA forwarding setting (ForwardingSmtpAddress) |
Yes |
No |
Yes |
|
Block forwarding set by the admin using EAC (ForwardingAddress) |
No |
No |
Yes |
|
Block forwarding using Power Automate / Flow |
No |
No |
No |
|
Does the sender get NDR when auto forward is blocked? |
No |
Yes |
Yes |
|
Customization and granular control |
No |
Yes |
Yes |
What happens if auto forward is controlled in multiple places mentioned above?
One question we encounter frequently is, how all these techniques work together? What if auto forward is blocked in one of the above methods but allowed in another? For example, auto forward is blocked by a remote domain setting or a transport rule but allowed in Outbound spam filter policy; what happens? The answer to that is that a restriction in one place will restrict auto forward for all.
For example:
- Automatic forwarding is On (allowed) in the Outbound spam filter policy.
- Automatic forwarding is disabled for the remote domain.
Will the automatically forwarded message be blocked by the remote domain? Yes, remote domain would block automatic forward as would an Exchange transport rule.
Depending on what you want to achieve, you can use combination of above features. There’s no one size fits all option. You can implement all four options if you really want, depending on your requirement. For example, the remote domain option controls the recipient domain and comes handy if you want to restrict auto forwarding for all except a few external domains. Outbound spam filter policies on the other hand can control the sender. If you want to allow external auto forwarding for only a few mailboxes (users with genuine business requirements to configure automatic forwarding) and block external auto forwarding for everyone else, Outbound spam filter policy is most preferred. Or you can use combination of these two options if you want to allow auto forwarding only for few mailboxes and to only a few external domains. Here is another example which is slightly more complex:
Let’s say you have the following requirements:
- By default, automatic forwarding should be blocked.
- Automatic forwarding to an external domain contoso.com should be allowed for all users.
- Allow users Jack and Jill to also be able to forward to northwindtraders.com, but no one else.
There are multiple methods to achieve this, the following is one such solution:
- Keep the new external forwarding control under Outbound spam filter policy setting to “On”.
- Disable automatic forward for default * domain in remote domain setting.
- Create a new remote domain for contoso.com and northwindtraders.com and allow automatic forward for these remote domains.
- Create a transport rule to block auto forward from all to northwindtraders.com but put an exception for users Jack and Jill.
- As transport rule will not block forwarding set using Outlook on the web (ForwardingSMTPAddress parameter) you can use RBAC rule to stop users from creating auto forward setting from OWA.
But wait, there is more!
To protect you further from attackers if a user mailbox is compromised (and for whom external automatic forward could be enabled without their knowledge), a new Email Forward Alert Policy has been released recently which is available under Alert Policies of our Security & Compliance portal. It is called “Suspicious Email Forwarding Activity.” This new alert will track all “forwarding scenarios” and detects when a user has automated the sending of messages external to the organization. Once we find any suspicious activity, we will alert the tenant administrator once per day as long as the user continues to forward to that external recipient. This policy has a Medium severity setting. Although it is rare, an alert generated by this policy may be an anomaly. Administrators should always check to confirm whether the user account is compromised. A screenshot of the policy:
A sample alert sent to the administrator:
That’s it for now! Hope you find this helpful. I also want to take a moment to thank Mike Brown, Nino Bilic for reviewing this.
Source link