
[ad_1]
————————————————————
Hi everyone!
The Conditional Access overview is a built-in dashboard that offers a comprehensive view of your Conditional Access posture. As an administrator, it provides a concise summary of your policies, identifies any gaps in your policy coverage, and provides valuable insights based on sign-in activity within your tenant. This feature enables you to swiftly pinpoint areas where you can enhance the enforcement of Zero Trust principles, ultimately bolstering your defense mechanisms.

The dashboard is now the default landing page of Conditional Access. As the first entry point into Conditional Access, the overview page lets you quickly create new policies using one of the Conditional Access templates which capture commonly used policies and best practices.
The dashboard also offers the following insights and reporting capabilities:
- The “See all unprotected sign-ins” link under the Users tile helps you rapidly identify users that are signing in without the protections of a Conditional Access policy.

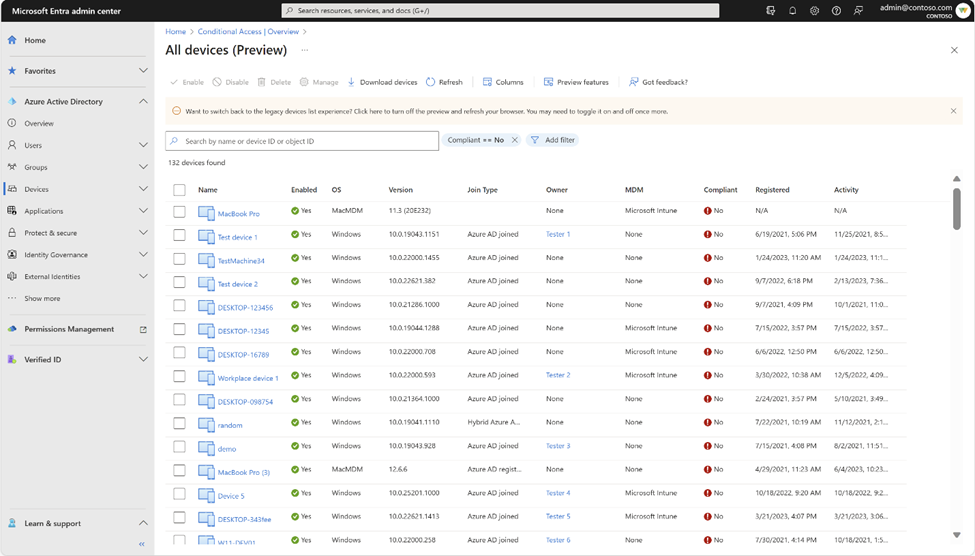
- The ‘See all non-compliant devices’ and ‘See all unmanaged devices’ links under the Devices tile help you identify device compliance gaps.
- You can discover the top 10 most accessed apps without Conditional Access coverage using the coverage tab and go one step further and identify the users without coverage for that app by clicking on the numbers in the ‘Users without coverage’ column.

You can discover security alerts generated based on sign-in activity in your tenant and take quick action on the alerts by deploying recommended zero trust conditional access policies using the Conditional Access templates. Speaking of which, let’s take a brief walkthrough of Conditional Access templates.
Conditional Access templates are a pre-defined set of conditions and controls that provide a convenient method to deploy new policies aligned with Microsoft recommendations. Customers are assured that their policies reflect modern best practices for securing corporate assets, promoting secure, optimal access for their hybrid workforce.
Conditional Access templates are organized across five scenarios:
- Secure foundation
- Zero Trust
- Remote work
- Protect administrators
- Emerging threats
Organizations can choose from 16 predefined Conditional Access templates based on their specific needs. Here is an example!
With the “Require phishing-resistant multifactor authentication for admins” Conditional Access template, customers can reduce the risk of compromise and phishing attacks on privileged users. This powerful template uses Conditional Access authentication strengths to help you choose the right authentication method requirements for specific scenarios, making it easier than ever for organizations to move their most critical users towards more secure, modern, and strong authentication.

Learn more about the Conditional Access overview dashboard: https://aka.ms/CAOverviewDashboard
Learn more about Conditional Access templates: https://aka.ms/ConditionalAccessTemplateDocs
Tell us what you think
Give it a try and let us know if you have questions or feedback at https://aka.ms/AzureADFeedback. We hope you will love it as much as we do!
Krishna Venkit
Product Manager
Microsoft Identity Division
Lisa Huang-North (@lisaychuang),
Senior Product Manager
Microsoft Identity Division
Learn more about Microsoft identity:
[ad_2]
Source link




