
[ad_1]
We’re only weeks away from Enterprises during the preview period are issuing and verifying credentials across a variety of scenarios, ranging from remote onboarding at work and collaboration across business boundaries to enabling education beyond the campus.
“Identity proofing by leading identity verification partners, in the form of Verifiable Credentials, will help reduce the remote onboarding time for our new employees from as much as 3 days [today] to as little as 10 minutes—all while improving the employee experience and making a great ‘first’ impression!” – Autodesk
I’m thrilled to share additional preview features aimed at making it easier for issuers and verifiers to exchange credentials in a trustworthy manner. As described in our previous blog post, we’re extending these new capabilities for any Microsoft customer.
What’s new
Quickly issue a Verifiable Credential for directory-based claims
Based on customer feedback, in addition to managing Custom Credentials, we’re excited to share that you can now use the Quick Start option to configure the look and feel based on directory-based claims. Directory-based claims (e.g., Azure AD) have been used to power profile cards in M365 for a long time. You can configure and tap into these claims using Microsoft Graph to create Verified Credentials for a wide variety of use cases, such as a verified employee.
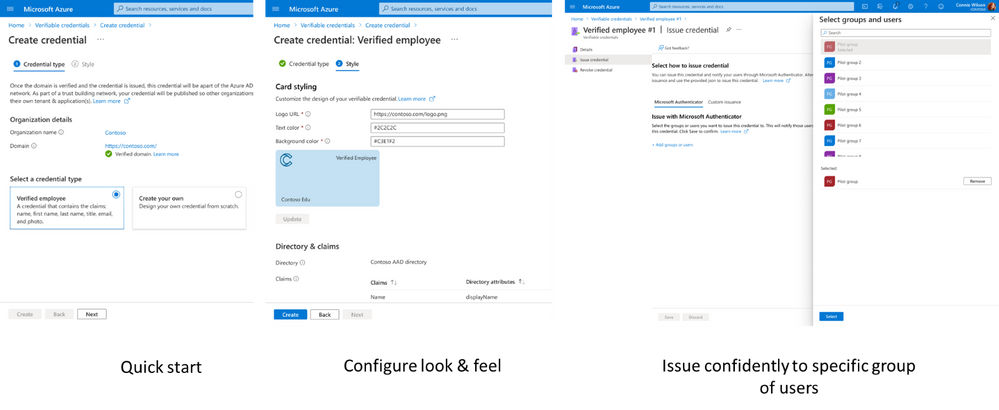
Enterprises can issue Verifiable Credentials to existing users of Microsoft Authenticator (or any other standards-compliant wallet). Admins can enable Authenticator users to accept these credentials with just one click!
Verifiable Credentials Network
We are thrilled to offer Verifiable Credentials Network so developers can discover their preferred issuer of credential types, e.g., Verified Student by Contoso University using portal for administrators or APIs. Anyone using the free version of Azure AD can now easily request and verify credentials without requiring any custom integration with issuers.
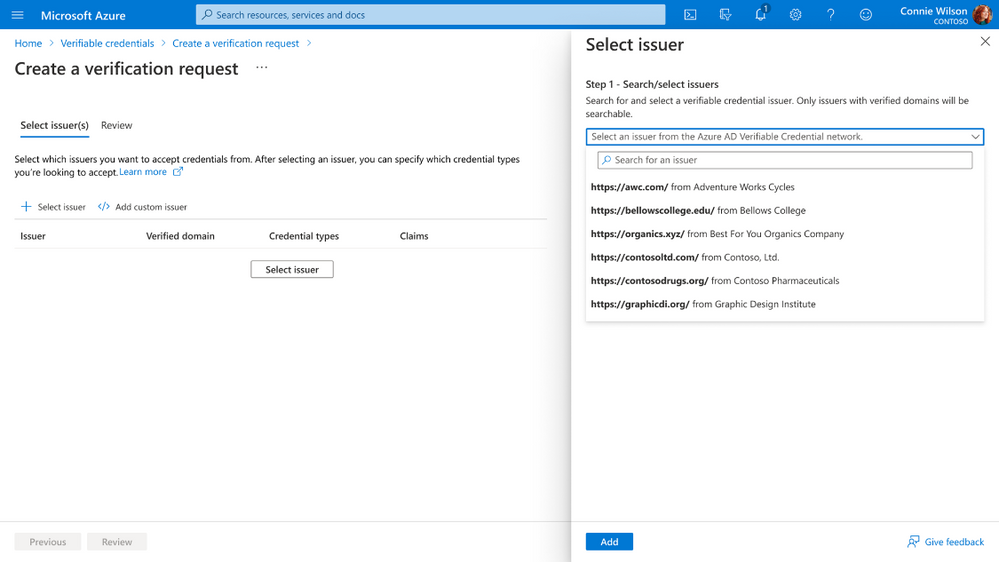
APIs for developers and administrators
Developers can use APIs for Verifiable Credential Network to discover credential types and choose their preferred issuer (e.g., student ID credentials by Contoso University). In addition, developers can use Request API to programmatically issue and verify credentials so developers can quickly integrate verifiable credentials into new and existing apps. Samples are available in .net, Java, Node.JS, and Python, illustrating how to use the Request API. In addition, using the Admin API, administrators can automate everything from onboarding your tenant to creating issuers, to managing the look and feel of credentials.
Recovering from loss of device using backup and restore

MS Authenticator users can now recover Verifiable Credentials in the event of a loss of device. Users can export their credentials and secure the exported file using a pass phrase to ensure that only you can access your encrypted credentials. If you lose your phone, you can use Microsoft Authenticator on the new device to import credentials using the file, along with the passphrase.
Thank you for your feedback
We enjoy hearing thoughts and reactions from the community, so please let us know what you think in the comments below, on Twitter (@AzureAD) or in the Azure Feedback Forum. Please check out documentation for further details.
Getting started
Learn more about Microsoft identity:
[ad_2]
Source link




